HPE Demos on Demand

Demos on Demand
Guest Speakers
- Richard Stiennon, Chief Analyst of IT Harvest
- James Morrison, Cybersecurity Technologist of HPE
What will you learn?
- Work From Home Vulnerabilites
- Remote Workforce Security
- Cybersecurity advice for customers
- HPE Solutions
- Solutions for Small and Medium Businesses
HPE Cyber Security Best Practices
HPE Cyber Security Best Practices to Protect Your Business
Are you truly prepared to protect your business from a cyberattack in times of uncertainty?
View this HPE Technical Whitepaper to learn more about HPE InfoSight Security for Storage Solutions
Featured Products
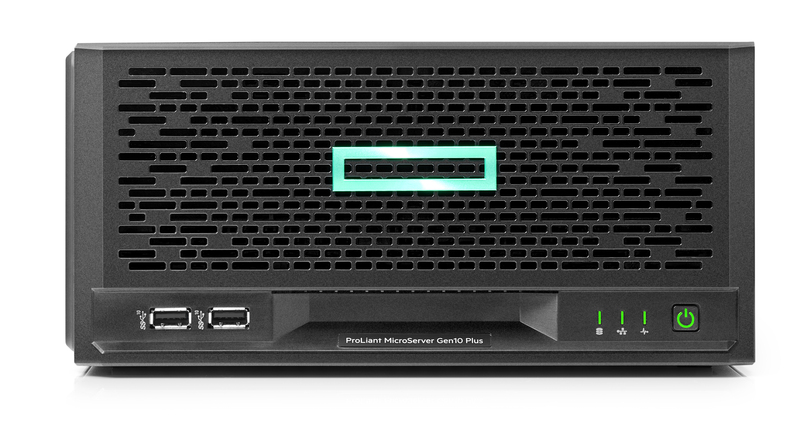
HPE ProLiant MicroServer Gen10 Plus
The HPE ProLiant MicroServer Gen10 Plus delivers an affordable compact yet powerful entry level server that you can customize for on-premises or for hybrid cloud possibilities. It is the most compact MicroServer that we have launched so far, which can be placed flat or vertically depending on your space.
HPE Nimble Storage All Flash Arrays
HPE Nimble Storage All Flash Arrays combine a flash-efficient architecture with HPE InfoSight predictive analytics to achieve fast, reliable access to data and 99.9999% guaranteed availability.
HPE Nimble Storage Adaptive Flash Arrays
The HPE Nimble Storage Adaptive Flash Arrays are like having two flash arrays in one. The array is truly adaptive – designed for both primary and secondary flash workloads.
Solutions and Resources
Rapidly Deploy Virtual Desktop Infrastructure (VDI) with HPE
Today exceptional circimstances have threatened businesses in every industry, interrupting critical daily business requirements. Customers are looking to rapidly unleash mobile productivity using VDI. HPE is committed to prioritizing the delivery of the worlds most secure platform to meet these critical demands.
HPE InfoSight for Servers
HPE InfoSight for Servers combines the machine learning and predictive analytics of HPE InfoSight with the health and performance monitoring of Active Health System (AHS) and HPE Integrated Lights Out (iLO) to optimize performance and predict and prevent problems.
Silicon Root of Trust
The Silicon Root of Trust satisfies organizations’ need for a robust security foundation that permits only trusted firmware to be loaded onto the server, and that can rapidly mitigate the impact of firmware attacks. It is able to recover itself from attacks by malicious code to a known and secure state, with trusted firmware, and without manual intervention.
Marsh's Cyber Catalyst Designation
Cyber Catalyst by Marsh is a ground-breaking way for organizations to make more informed choices about cybersecurity products to help reduce cyber risk.